The online privacy of veterans and Veterans Affairs employees—including their health-care and financial information—is at risk, according to an internal draft of a VA report obtained by CNBC.
A data breach to financial, medical and personal information is "practically unavoidable" and is likely to happen within 12 to 18 months, according to the draft report prepared in July by the VA's Office of Information & Technology Risk Management Team. The office is responsible for securing the online data of roughly 20 million American veterans, dependents and VA employees.
"The VA cannot ensure the safety and privacy of Veteran and employee healthcare, benefits, and financial information," according to the July 2, 2013, report. "The VA is non-compliant with its own privacy and security policies and with Federal laws and regulations."
VA spokeswoman Victoria Dillon told CNBC in an email, "The internal VA document referenced was an internal draft document with significant inaccuracies that was subsequently rescinded and corrected. The final document no longer contains the quoted inaccurate language."
When asked which specific portions of the report were inaccurate, Dillon failed to respond. Follow-up questions through additional emails and phone calls for an updated report were not returned.
In a May letter obtained by CNBC, Secretary of Veterans Affairs Eric Shinseki vouched for the VA's information technology systems. "To be clear, VA's security posture was never at risk," Shinseki said in the letter to Rep. Mike Coffman, chairman of the House Veterans Affairs Subcommittee for Oversight and Investigations.
(Read more: VA use of implants target of probe, report says)
In addition to the July report, separate testimony on June 4 before the House Committee on Veterans' Affairs called into question the security of veterans' information.
"In nearly 20 years of building and managing security programs across government and private industry, I had never seen an organization with as many unattended IT security vulnerabilities," said Jerry Davis, former deputy assistant secretary for information security at the Department of Veterans Affairs.
The June hearing also revealed the VA had been hacked by multiple foreign entities since March 2010.
(Read more: University ofMaryland reports massive data breach)
Two VA officials specializing in information technology, Stephen Warren and Stan Lowe, testified that at least one foreign entity had targeted and penetrated the VA's network, according to testimony shared during the hearing.
Asked during the hearing whether or not VA has identified more than one foreign entity that has penetrated the network, Lowe, now VA deputy assistant secretary for information security, responded, "Yes, sir."
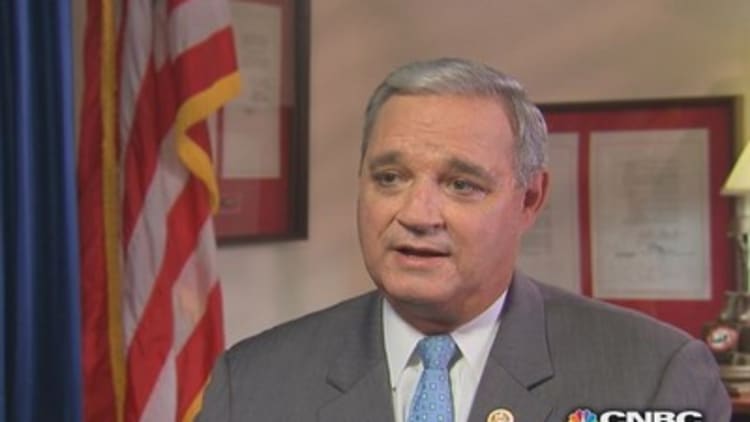
Coffman, R-Colo., said during the hearing that evidence suggests the VA's database "has repeatedly been compromised since 2010 by foreign actors, including in China and possibly in Russia."
There have been at least eight breaches of VA's network since March 2010, including the "Master Password" file that had been compromised, according to testimony during the hearing.
"VA takes seriously its obligation to properly safeguard any personal information within our possession," Dillon told CNBC in an email. "VA has in place a strong, multi-layered defense to combat evolving cybersecurity threats. VA is committed to protecting Veteran information, continuing its efforts to strengthen information security, and putting in place the technology and processes to ensure Veteran data at VA are secure."
In a November documentary, CNBC reported about major problems within the VA health-care system, including preventable patient deaths and unsterile conditions at hospitals where big bonuses were given to officials.
(Read more: Death & Dishonor - Crisis at the VA)
—By CNBC's Dina Gusovsky. Follow her on Twitter @DinaGusovsky.


